We were contacted late in the day yesterday by someone who's site had been hacked.
It was covered in ads and the site itself wouldn't even load. It simply showed a blank white page with ads on it. This site was a WordPress site. We discussed with the owner how much it would cost to fix, as well as explained how our ongoing maintenance plan would probably be more bang for his buck. The client agreed to ongoing maintenance and here's kind of a breakdown of what we did to resolve his woes, and get his business site back up and running.
We got to work quickly, backing up the existing infected site - so we'd have a base version to compare files to. Then we began running our security scanning tools on the site and repairing the damage that the hacker did.
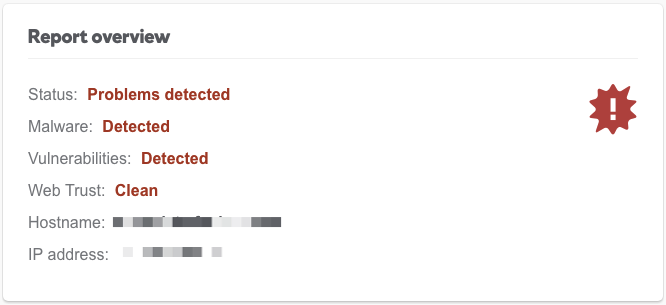
Malware Detected!
Our Security Scan right away found Malware and vulnerabilities with the site.
The Hackers had injected PHP code throughout the site causing the site to display the ads. In addition they actually removed the site owner's Admin account.
Since the owner of the site didn't have any access to his WordPress Admin anymore he wasn't able to give us an account to get in and fix the site. We broke our way into the site by adding a PHP file through SFTP that would create a new admin user account for us. Once in we saw all of the plugins were using outdated versions and the WordPress core was also on an old version. Keeping your site's software up-to-date is critical to site security.
The versions of the software were too out of date to risk just updating them and hoping for the best, as the front end of the site could get screwed up by such a large jump in versions.
In order to play it safe we employed a "safe backup" procedure, where took a backup and screenshot before updating the wordpress core to the latest version, then we did the same for each plugin updating the core, and then each plugin individually. Then we compared each page of the site to the screenshot to ensure nothing went wrong. If something did go wrong we would have reverted to the backed-up version of the site taken just before that specific plugin was updated, and avoided updating that plugin.
We then went through the content of the pages and found the hackers had used a database injection to inject links directly into the WordPress content. Since they used that method to add their spam, it didn't affect the Wordpress revision history.
Revision History
Because it didn't affect the history we were able to revert to the previous version and show content exactly as it was before the hack.
We then ran across some issues with some of the plugins being paid plugins that were out dated. We purchased a new license in order to update to a newer version of the plugin without breaking the functionality of the plugins.
All in all we had this done rather quickly, and the client has some any purpose hours left to call upon us to make changes to their site.
Has your site been hacked? Tell us about it through our contact form, we'd love to help you out.